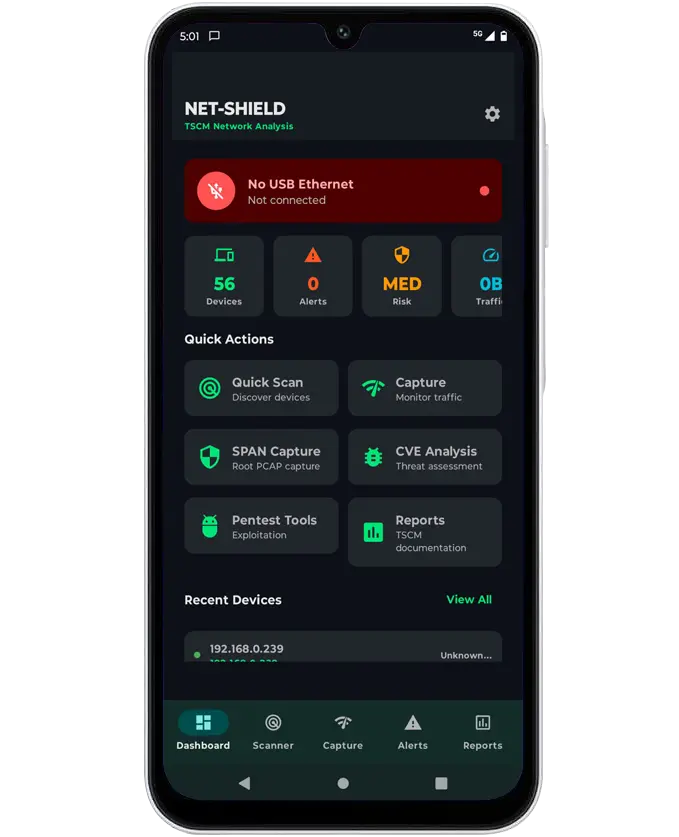
Net Shield
TSCM network security analysis app
It takes a super snap shot of all networked devices. Allowing for real-time or post processing of network analysis and threat assessment

Instant Network Intelligence.
Net Shield delivers an instant snapshot of every device on your network, leveraging deep-level analysis to expose hidden threats that standard tools miss.
Whether you are conducting a TSCM sweep, investigating a potential breach, or performing routine network security audits, Net Shield provides the actionable intelligence you need to secure your infrastructure.
Core Features
Instant Network Snapshot
Captures a comprehensive snapshot of all connected network devices and active services within seconds, enabling immediate visibility during an operation or detailed post-analysis after deployment.
Device Discovery & Identification
- Rapid discovery of wired network devices
- Identification of device type, vendor, and exposed services
- Risk indicators to prioritise further investigation
Designed to quickly highlight unknown or unauthorised devices connected to a network.
Passive Traffic Monitoring
- Real-time visibility of network behaviour without disrupting traffic
- Monitoring of protocol activity and communication patterns
- Detection of abnormal or suspicious network behaviour
Ideal for use in sensitive environments where active interference is not permitted.
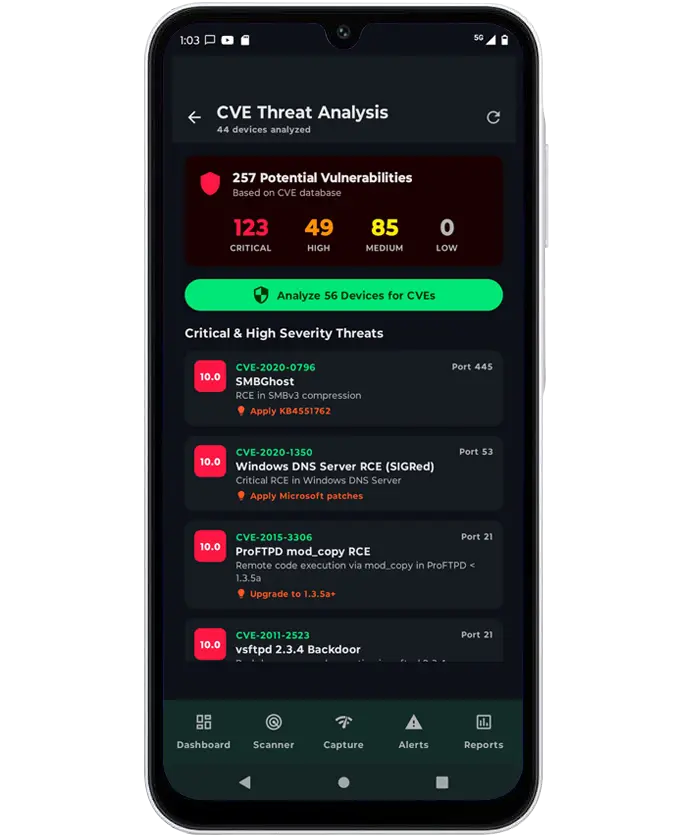
Threat & Anomaly Detection
Identifies indicators commonly associated with covert activity, including:
- Suspicious beaconing and outbound communication patterns
- Network manipulation attempts (e.g. spoofing behaviours)
- Unusual service exposure and tunnelling indicators
Supports informed decision-making during security assessments.
Portable Wired Network Access
- USB-Ethernet (OTG) support for rapid on-site deployment
- Compatible with common Ethernet adapters
- Allows access to environments where Wi-Fi is restricted or unavailable
Extends TSCM capability into wired network infrastructure.
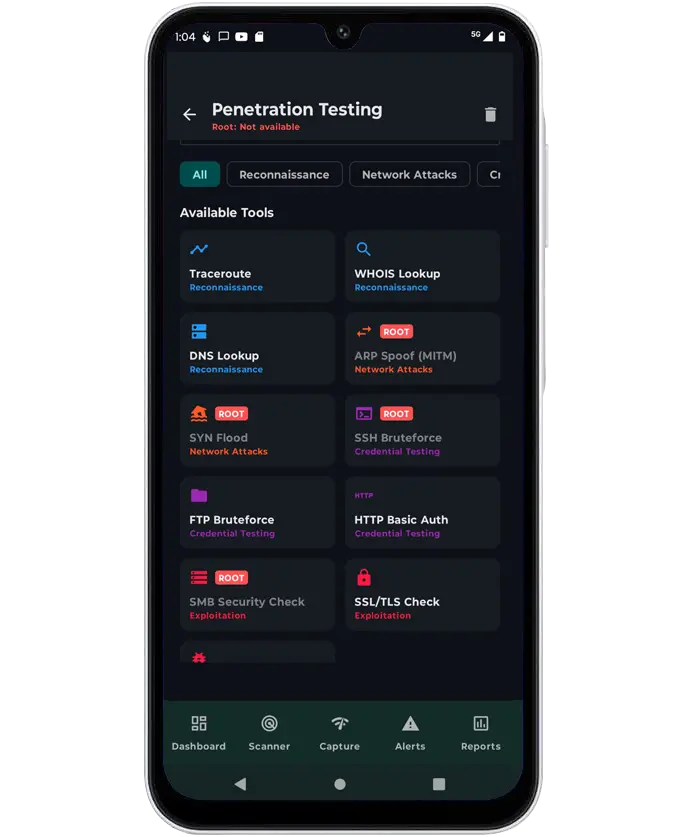
Advanced Packet Analysis (Authorised Use)
- Supports deeper packet-level inspection in controlled environments
- Enables detailed traffic review and forensic post-processing
- Designed for authorised operators with appropriate permissions
Reporting & Documentation
- Built-in tools to document devices, alerts, and findings
- Generate structured reports for internal review or client delivery
- Supports audit trails and operational documentation
Deployment & Requirements
- Flexible Android Deployment Operates on Android 8.0+ devices with USB-OTG support, suitable for rapid field use.
- No-Root Baseline Capability Enables full network discovery, port scanning, passive traffic monitoring, anomaly detection, and reporting without root access.
- Advanced Analysis (Optional) Rooted devices unlock deeper packet capture, filtered traffic inspection, and extended diagnostic utilities.
- Field-Ready by Design Optimised for portable network inspection, on-site threat assessment, and post-event analysis.