
TSCM for the Digital Age
Beyond simple detection. Acustek delivers absolute protocol intelligence for real world digital signals down to device level.
Beyond Detection. Absolute Protocol Intelligence.
In an era where surveillance threats hide within encrypted WiFi bursts, hopping Bluetooth signals, and complex cellular networks, traditional "analog" hunting is no longer enough. While legacy superheterodyne receivers listen for noise, Acustek decodes the environment.
We provide the tools to see through the digital fog, turning invisible signals into actionable intelligence.
Evolution, Not Just Innovation
Acustek was founded in 2009 with a singular mission: to provide elite security professionals with the most reliable technical surveillance countermeasures on the market. We aren't a venture-backed newcomer or a "fly-by-night" startup chasing a trend. We are a hard-working team of engineers and specialists who have spent over 15 years perfecting our technology.
Our journey has been one of relentless iteration. From our headquarters in Dublin, we have spent more than a decade-and-a-half working alongside government agencies and global corporations. Every piece of hardware we ship today—including the revolutionary Dark Compass—is the result of years of field-tested feedback and constant refinement. When you choose Acustek, you are choosing a partner with a long-standing heritage of engineering excellence.
Why Modern Threats Require a New Standard
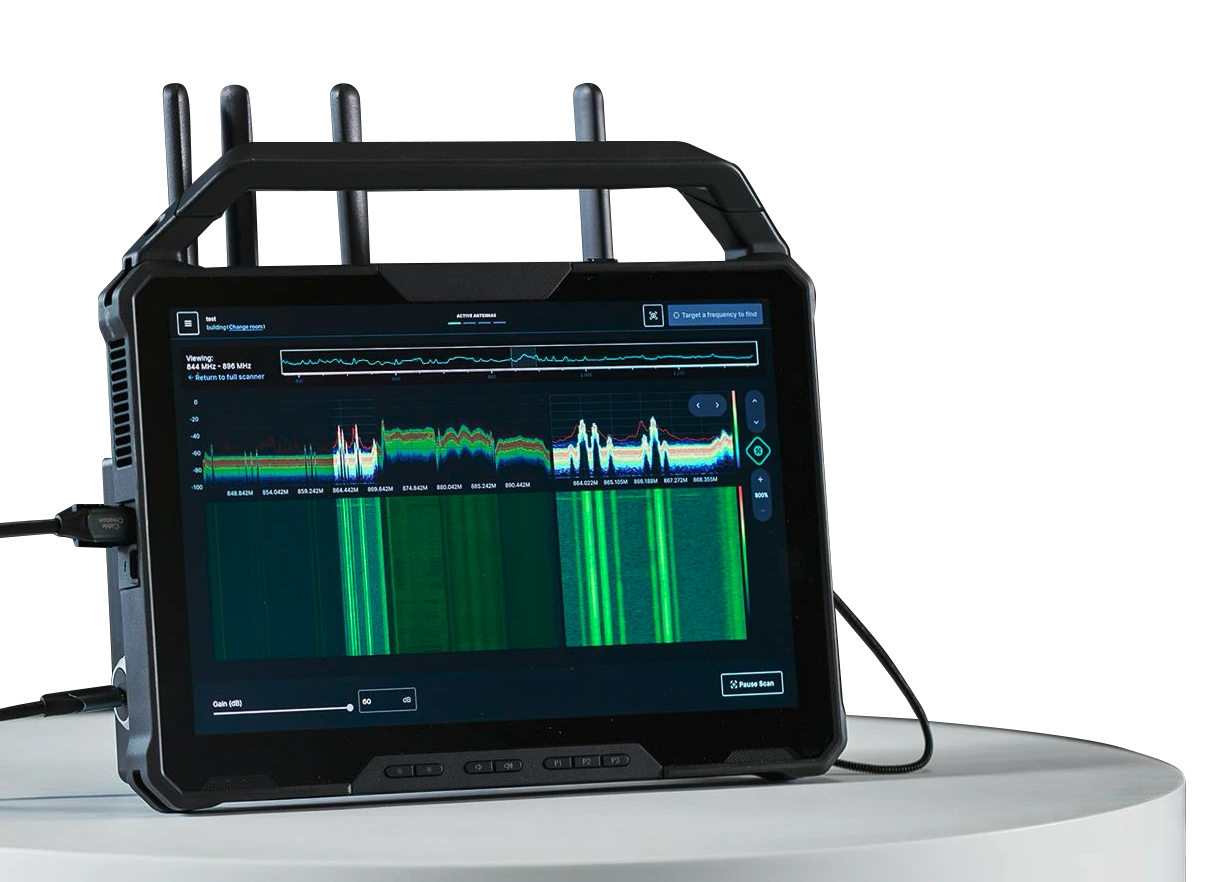
The "Old Way" of sweeping relied on detecting simple energy spikes. Today's threats are smarter, stealthier, and fully digital. Acustek's ecosystem is built specifically for this new reality.
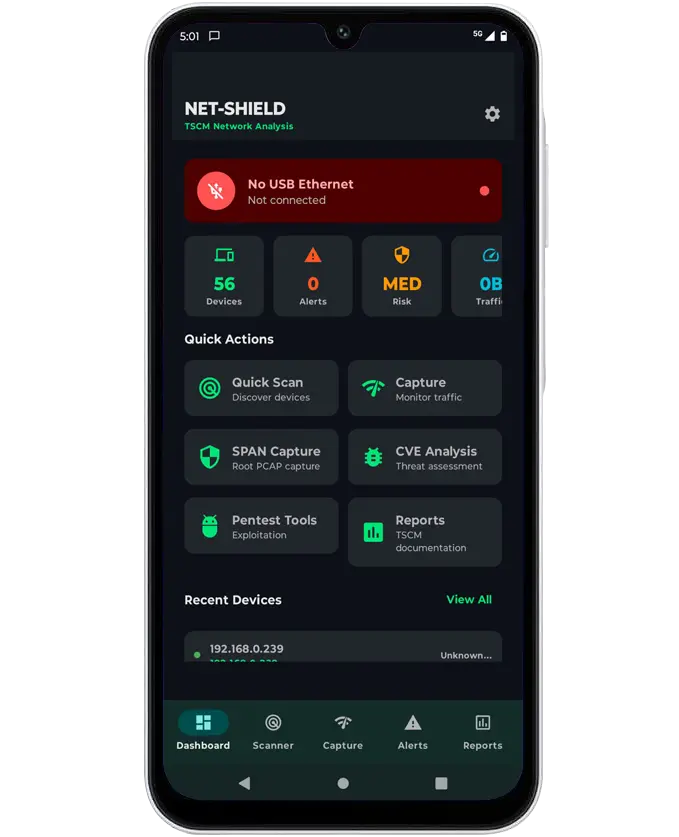
- Deep Protocol Analysis: We don't just find a signal; we identify it. Our systems interrogate the environment to provide MAC addresses, SSIDs, and device fingerprints for WiFi and Bluetooth.
- Visual Direction Finding (DF): Move past the guesswork of "hot and cold" signal hunting. Our visual localization tools point you directly to the source of a threat in real-time, significantly reducing sweep times.
- Forensic Reporting & Visualizations: The end-product of any sweep is the report. We provide high-fidelity visual data—including constellation displays and time-stamped logs—that turn complex technical data into clear, professional proof for the boardroom.
The Acustek Difference: Legacy Expertise Meets Future Tech
| Features | Legacy System | Acustek Digital-Age TSCM |
|---|---|---|
| Detection Method | Analog Energy Detection | Digital Packet & IQ Vector Analysis |
| Signal Depth | Frequency Only | Protocol Identity (SSID, MAC, etc.) |
| Localisation | Signal Strength Audibles | Visual Heat - Mapping & Direction Finding |
| History | Legacy Giants or New Startups | Proven Field-Expertise Since 2009 |
| Reporting | Manual/ Handwritten Logs | Automated Forensics - Grade Visual Reports |
Bridge the Gap Between Analog and Digital
Don't rely on 20th-century tools to fight 21st-century threats. Trust the team that has been evolving alongside the threat landscape for over 15 years.
Signal Threat Detection & RF Analysis
For detecting unknown, suspicious or covert wireless activity.
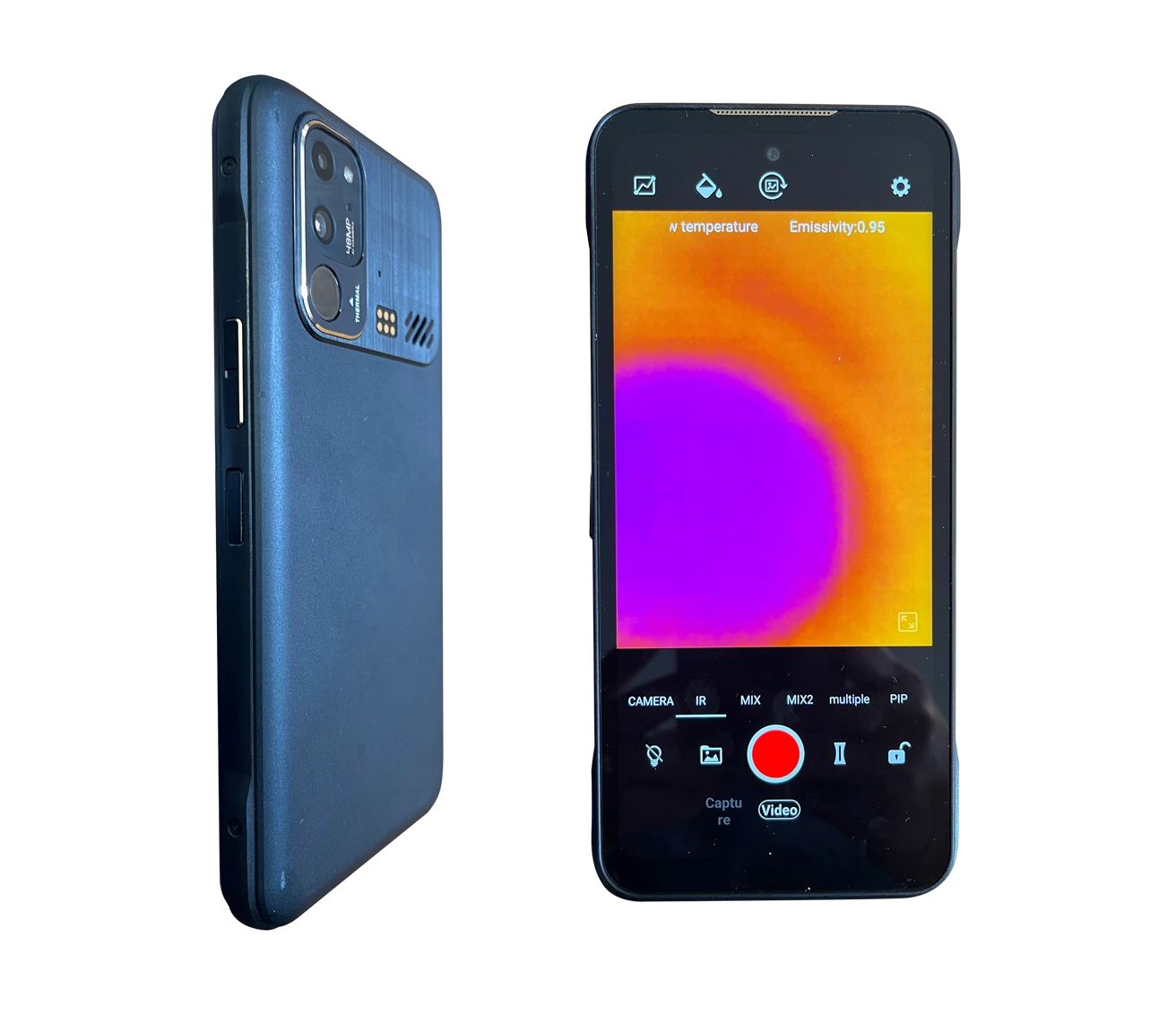
Thermal & Visual Inspection
Reveal heat signatures, hidden compartments and concealed electronics.
Hidden Electronics Detection
Identify electronic circuits—even when powered off.
Secure Conversation Protection
Block microphones to prevent audio capture during sensitive meetings.
NextGen Countermeasures All-In-One Kit
A complete threat-response package for high-risk environments.